Introduction
Motivation
Contributions
Review of Literature
Methodology
Data Collection and Pre-processing
FHE-based Authentication, Signatures, and Access Control
FHE Configuration for Privacy-Preserving Neural Inference
Permissioned Blockchain Framework for Secure EHR Orchestration
Deep Learning as a Service (DLaaS) on Encrypted EHR Trajectories
Security and Compliance Status
Implementation Details and Reproducibility
Performance Evaluation
System Workflow and Interaction Model
Communication Costs Metrics
Results Analysis and Discussion
Security and Computational Analysis
Initialization Stage
Discussion
Conclusion and Future Work
Declarations
Introduction
Healthcare 4.0 is driving a paradigm shift toward networked, analytics-driven healthcare ecosystems that are increasingly embedded within smart buildings and sustainable urban environments. In this transformation, Electronic Health Records (EHRs) serve as a critical digital infrastructure, supporting healthcare delivery across hospitals, diagnostic laboratories, insurance services, and telemedicine facilities integrated into modern building systems. EHRs consolidate diagnostic findings, clinical procedures, medication records, and longitudinal patient histories, enabling efficient and coordinated care delivery [1]. However, as healthcare services expand across interconnected facilities and urban healthcare networks, new risks emerge regarding the accessibility, privacy, and governance of sensitive medical information. These challenges are particularly significant in sustainable healthcare buildings, where secure digital interoperability is essential for facility management, occupant well-being, and real-time decision-making. Addressing these risks is therefore essential to ensure resilient, trustworthy, and sustainable healthcare services within smart building and urban healthcare infrastructures [2].
When it comes to protecting information during storage or transmission, the standard methods like data at rest encryption and access control are usually used, which also needs to decrypt data for processing. Because of this, there is a large window of vulnerability when analytics and decision-support algorithms can work with decrypted data, making healthcare systems vulnerable to either insider or external attacker exploitation [1]. Consequently, the requirement for an inherent secure framework has emerged with Healthcare 4.0’s development [2].
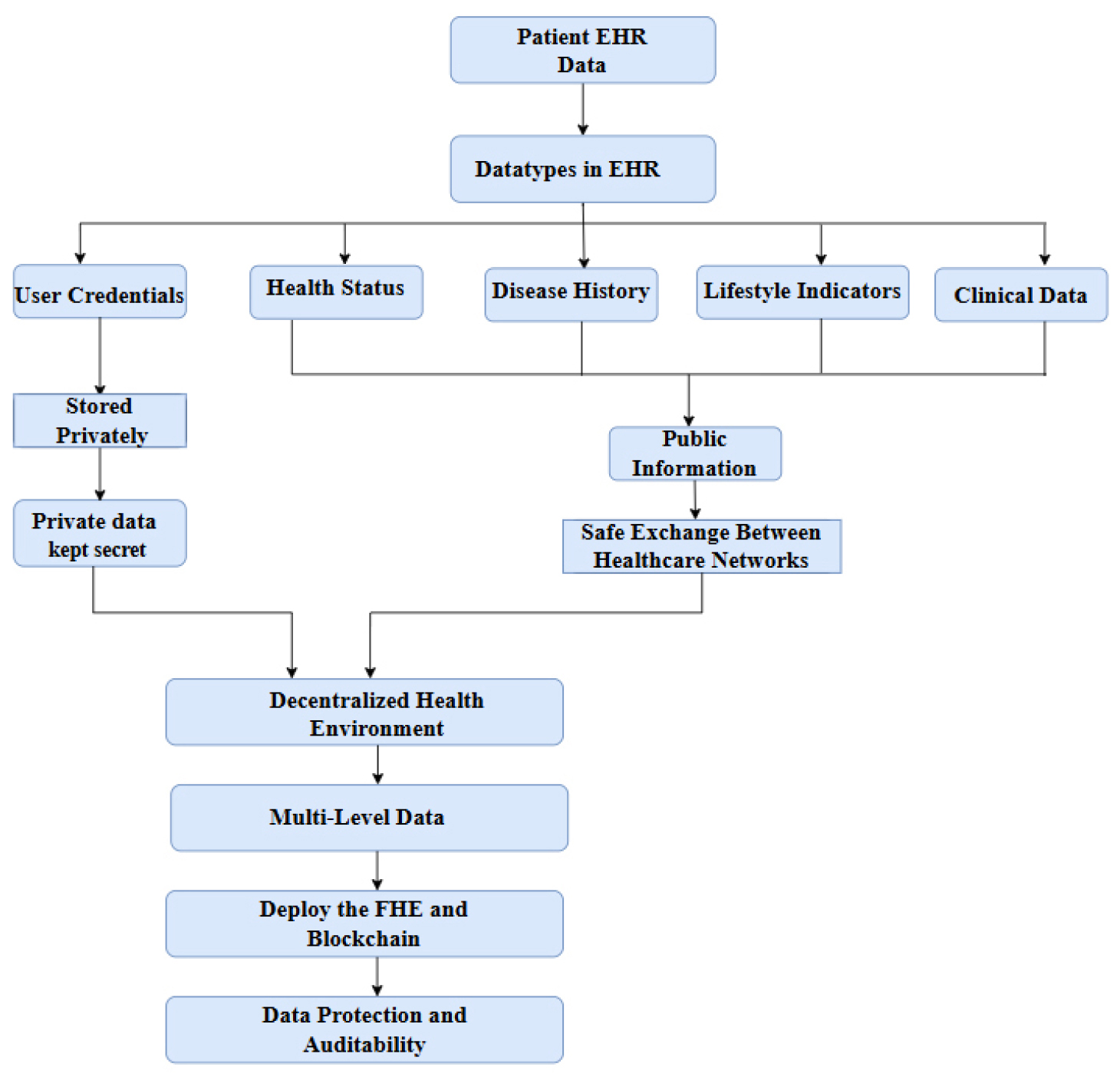
The planned Healthcare 4.0 ecosystem’s data structure is shown in Figure 1, including the processing of EHR sections according to their sensitivity. First, patient data is categorized into highly sensitive parts, such as credentials and keys, and general information, such as abstracts and non-identifying indicators. Highly sensitive parts should be stored in private storage, while sharable parts should be arranged for sharing in regulated manners among all the participants within healthcare. Thereafter, the process goes on using FHE to encrypt data for analytics confidentiality and blockchain technology for tamper- evident recordkeeping.
Blockchain has received considerable attention in research for enhancing integrity, traceability, and decentralized management for health data management. By allowing the maintenance of an immutable ledger and by granting accessibility to smart contracts for management, blockchain facilitates tamper-proof audit trails and reduced dependence on one central point of control [3]. Nonetheless, blockchain by itself can not provide data confidentiality, as the transparency of the ledger and transaction metadata can reveal sensitive information [4]. Moreover, several blockchain-based EHR systems employ end-to-end encryption solely at the storage level while doing analytics in plaintext [5].
Fully Homomorphic Encryption (FHE) permits mathematical operations to be executed directly on ciphertexts, ensuring that EHR data remains encrypted during the calculation process [6]. This is actually very fundamental when it comes to privacy-preserving healthcare analytics because the party offering the services should not have access to the medical data or the intermediate attributes [7]. Nonetheless, FHE by itself fails to tackle the multi-stakeholder coordination, access governance, and auditability demands intrinsic to healthcare consortia [8].
Motivation
Implementations of Healthcare 4.0 in healthy and sustainable smart buildings necessitate ongoing, multi-stakeholder data exchange across hospitals, diagnostic laboratories, insurers, and outsourced analytics firms; yet, current protection systems are disjointed. Traditional EHR systems generally encrypt data both at rest and in transit; however, they subsequently decrypt it for decision support and predictive modeling, resulting in a vulnerability period during which sensitive records and intermediate features may be accessible to insiders, compromised infrastructure, or untrustworthy service providers. Blockchain-based healthcare solutions enhance integrity and traceability; nevertheless, they do not mitigate confidentiality breaches via transaction metadata and frequently depend on plaintext analytics. Fully Homomorphic Encryption facilitates computation on ciphertexts; however, standalone FHE fails to resolve the practical deficiencies required for actual implementations, specifically consent enforcement, auditable governance, and coordinated access control among disparate entities. These deficiencies necessitate a cohesive framework that concurrently delivers encrypted predictive analytics, tamper-evident accountability, and policy-enforced data access appropriate for decentralized Healthcare 4.0 smart building settings.
Contributions
∙This study introduces FHEDaaS, a comprehensive Healthcare 4.0 platform that consolidates CKKS- based homomorphic encrypted inference, permissioned blockchain governance, and smart contract- driven access control for electronic health record sharing in smart building environments.
∙Creates a privacy-preserving Deep Learning-as-a- Service framework that facilitates encrypted illness prediction across longitudinal electronic health record trajectories with a BiLSTM model, while safeguarding against plaintext disclosure during outsourced inference.
∙Establishes a permissioned consortium ledger that documents cryptographic commitments, consent metadata, and verifiable access decisions, while maintaining encrypted electronic health record payloads off-chain for enhanced scalability.
∙Delivers a comprehensive system-level assessment encompassing predictive performance and overhead, including latency analysis spanning plaintext inference, FHE-only inference, and complete FHEDaaS execution with blockchain authorization and commitment.
∙Documents the time of cryptographic primitives and validates CKKS parameters (security configuration supported by estimators) to facilitate reproducibility and transparent evaluation of the privacy- performance trade-off.
The subsequent sections of this work are structured as follows. Section 2 offers an extensive examination of pertinent literature on blockchain-based healthcare systems, homomorphic encryption in medical analytics, and privacy-preserving deep learning frameworks. Section 3 delineates the proposed FHEDaaS architecture, encompassing the Healthcare 4.0 tiered system concept, CKKS-based encrypted inference workflow, smart contract governance mechanism, and implementation parameters. Section 4 presents the experimental findings, encompassing predictive performance evaluation, latency ablation, throughput analysis, cryptographic overhead assessment, and validation of security parameters. Section 5 concludes with a summary of the principal findings, examines practical implications for the implementation of Healthcare 4.0 smart buildings, and delineates avenues for further research.
Review of Literature
Several individuals have contemplated the interplay between electronic health records and blockchain technologies in recent years. Systematic reviews reflecting the relevance of their combination have been discovered in the literature. The use of blockchain technology in the EHR system helps in enhancing the transparency, privacy, security, ease of management, and ease of usage [9]. This field of knowledge has shown productivity in its development since it was able to produce a total of 130 articles in 2023. It can thus be concluded that interest in the healthcare aspect using blockchain technology is on the rise [10].
The use of blockchain technology in healthcare has been the subject of several comprehensive assessments in the last few years, with a total of 3800 records in Scopus, a total of 1383 records in IEEE Access, and a total of 537 published papers in PubMed as of September 2023 [11]. This guarantees the confidentiality and security of the EHR system, while eliminating central failure and susceptibility to assaults, owing to the encryption capabilities and decentralized characteristics of blockchain technology [12]. Studies after studies have shown that blockchain technology can address some of the most basic problems with health care data [13].
An all-encompassing blockchain system for healthcare data management has been the primary focus of the continuing research. Smart contract management is a key part of the cutting-edge design, the management of the privacy key, encrypting the healthcare data, the management of the healthcare blockchain network, and integration with the healthcare IT sector. These five components together enable health care organizations like “Medical Companies” to make patients’ data private and secure [14]. Blockchain, a decentralized ledger system composed of interconnected and secure data blocks, offers patients a promising and highly secure method and doctors to exchange medical information that would revolutionize hospital EHR administration [15].
The risks associated with the security of the former EHR systems are also well known. The attraction of cyber attackers to personal health records is due to the extent to which the information contained in this document is so private and can be embarrassing to the involved individual; as a result, the whole scenario is faced with utmost denial and defamation by the attacker; in addition to this, most of the individual and collective health information of patients is in the hands of a number of health providers, who in turn have different risks to health security, and the major one being the security risks due to hackings by a third party [16]. he health records in an electronic format have efficiency, health security, and reduced information redundance, although having different risks like the paper health records system [17].
Simultaneously, the application of homomorphic encryption has been on the increase within the field of medical computing. The application of cloud computing and cloud storage systems has significantly influenced the handling of data within this domain of opening resources to access, as well as the compromise of personal data to other service providers. Notably, this applies within the domain of digital health storage [18]. Homomorphic encryption is employed to safeguard personal data that is intended to be processed when the data is encrypted. Personal data within its encrypted form is the only data known to the service providers.
Homomorphic encryption has been classified in various ways according to the nature of the application; specifically, various classifications have been put forward by recent systematic analyses. Encryption types are categorized according to their degree of homomorphism: somewhat (PHE), somewhat (SHE), completely (FHE), and altogether leveled (FLE) homomorphic, together with the cryptographic frameworks pertaining to each one, with emphasis on the capability of HE in improving data security and privacy in the service industry [2]. Homomorphic encryption eliminates the requirement to decode data before performing calculations on it, thus being an effective approach in the feasibility study of data held in varied locations [19].
This brings in the applicability of the healthcare sector with homomorphic encryption significantly further. The latest research work incorporating the function using only Logistic Regression with homomorphic encryption showed equal results to algorithms using non-homomorphic encryption with a different results margin of only 1% to 3%, and equal speed and efficiency of usage [20]. The research attempted to investigate practical healthcare applications of Fully Homomorphic Encryption for its intersection mechanism, with an emphasis on quality control techniques as well as neural network models for diagnosis [21].
Conversely, the difficulties of applying homomorphic encryption to the health sector are obvious from the literature. While being very useful in healthcare, homomorphic encryption poses a problem of computationally expensive operations. Researchers are currently working on improving the algorithms and the implementation of algorithms into hardware to solve this problem, and the associated issues are also examined [7]. Homomorphic encryption is considered the most efficient and safest way to fix the issue of data privacy uses available data [22], The implementation in actual applications is constrained due to suboptimal performance.
A whole new field of research has emerged: the use of blockchain as well as homomorphic encryption in healthcare. Health Care 4.0 settings have not yet seen a comprehensive examination of blockchain-based electronic health record systems in conjunction with homomorphic encryption systems, despite the fact that both have been studied independently. Research on blockchain technology in healthcare has so far focused on data integrity along with access management, but has not yet included computations that guarantee patients’ privacy at a high degree. On the other hand, studies on homomorphic encryption concepts have given emphasis to computational privacy, whereas the distributed environment of the healthcare industry is not adequately considered as defined in Table 1[23, 24, 25, 26, 27, 28, 29, 30, 31, 32, 33, 34, 35, 36, 37, 38, 39, 40, 41, 42, 43, 44, 45, 46, 47, 48, 49, 50, 51].
Table 1.
Comparative studies of Model / Approach with Dataset
| Study (Year) | Model / Approach | Dataset | Findings | Limitation |
|
Naresh & Reddi (2025) [20] | HELR: Fully homomorphic logistic regression (CKKS via TenSEAL) on encrypted data | Heart disease datasets (Kaggle “Heart Disease”, Statlog Heart, Framingham) | HELR attained high accuracy (within 1–3% of non-HE model) and outperformed SVM; robust against various privacy attacks. | Heavy computation: encryption/decryption causes large overhead and poor scalability on big data. |
| Tawfik et al. (2025) – [23] | PriCollabAnalysis: Permissioned blockchain (Hyperledger) + secret-sharing + SMPC + additive HE (Paillier) for collaborative analytics | Synthetic healthcare records on a Hyperledger Fabric testbed | Privacy preserved and secure statistical analysis achieved; the framework balanced privacy and performance for practical healthcare use. | Trade-off: cryptographic methods (HE/SMPC) incur high overhead, limiting efficiency as data volume/complexity grows. |
| Gogoi & Valan (2026) – [24] | Review of HE schemes; Case Study: Paillier-encrypted logistic regression | UCI Heart Disease (public) | Encrypted inference achieved 90.16% accuracy (identical to plaintext) for heart-disease prediction, confirming HE can fully preserve utility. | Major computational cost: encrypted inference took minutes per query versus milliseconds in plaintext, highlighting a severe latency bottleneck. |
| Ali et al. (2025) – [25] | Health-FedNet: FL with Differential Privacy + HE (CKKS) + adaptive node weighting | MIMIC-III EHR (ICU clinical data) | ~12% higher diagnostic accuracy than a centralized model (p<0.01); supports real-time updates and meets HIPAA/GDPR privacy. | Evaluation limited to one dataset; practical deployment (cross-border training, edge/streaming data) and HE overhead not fully studied. |
| Wang et al. (2023) – [27] | PPFLHE: FL with Paillier HE + identity Access Control + ACK drop-handling | APTOS 2019 (retinal images), CIFAR-10 | High utility: achieved ~81.5% accuracy on encrypted image classification; reduced communication delay via dropout handling. | HE slows FL: encryption/decryption per round increases latency; AC/ACK adds protocol overhead. |
| Selvakumar & Senthilkumar (2025) – [28] | Quantized FCNN with TFHE encrypted inference | MedMNIST (medical image classification) | Encrypted inference accuracy 87.5% vs 88.2% plaintext; inference time ~150 ms/image. | Latency: ~150 ms per image (vs near-zero plaintext time) due to TFHE; only simple network used (FCNN), not complex CNNs. |
| Markkandan et al. (2024) – [29] | FL + Partially Homomorphic Crypto (PHC) + Residual Deep Belief Network | Multiple institution clinical datasets | Maintained/boosted diagnostic accuracy; ~10% average accuracy gain and ~30% reduction in communication overhead across institutions. | PHC cost: ~150 ms encryption delay and ~1000 ms model inference per sample, which may impede real-time use. |
| Ahmed & Hrzic (2025) –[30] | Literature review of blockchain+FHE hybrid for genomic sharing | N/A (theoretical review) | Conceptual hybrid aligns with ethics (accountability, fairness, privacy) in public health data sharing. | Scalability: computational overhead is the main barrier to real deployment, as noted by ethicists. |
Prior studies remains fragmented: blockchain-based electronic health record systems primarily provide integrity, traceability, and access logging, yet perform analytics in plaintext; homomorphic encryption for healthcare analytics maintains confidentiality during computation but is generally slow and inadequate for multi-stakeholder governance; and hybrid methodologies are frequently theoretical or assessed in limited environments, lacking comprehensive deep-sequence models, ambiguous security validation, and insufficient ablation studies to allocate overhead among encryption, inference, smart contract authorization, and ledger commitment. FHEDaaS addresses this deficiency by providing a comprehensive Healthcare 4.0 workflow that integrates CKKS-encrypted BiLSTM inference with permissioned blockchain governance, wherein smart contracts implement role- based policies and the ledger ensures immutable audit commitments, while computations are conducted solely in ciphertext. The platform additionally provides a component-wise evaluation (plaintext vs FHE-only vs full FHEDaaS) with specified CKKS settings, facilitating reproducible and realistic assessment of the privacy-performance trade-off for smart building implementations.
Methodology
This paper presents FHEDaaS, a Healthcare 4.0 framework designed for privacy-preserving healthcare analytics inside healthy and sustainable smart building environments. The system integrates CKKS-based Fully Homomorphic Encryption with a permissioned blockchain to safeguard Electronic Health Records while facilitating regulated sharing and verifiable access. The pipeline initiates with the secure ingestion and preparation of longitudinal EHR event streams, during which records are standardized, anonymised, and converted into sequential representations for temporal modeling. Patient trajectories are encrypted prior to outsourced computation, and smart contracts ensure consent and role-based authorization while preserving tamper-evident logs. A Deep Learning as a Service module then executes encrypted BiLSTM inference on ciphertext inputs. To ensure reproducibility and practical practicality, model training is conducted on anonymized plaintext data within a controlled environment, whereas inference during deployment utilizes FHE ciphertexts.
Data Collection and Pre-processing
Datasets
The experimental assessment employs two modern clinical sequence benchmarks: the SemEval-2024 Clinical Prediction Task dataset and the PROMISE-Eval 2024 dataset. Both datasets offer longitudinal Electronic Health Record timelines that conform to standardized clinical terminologies, including ICD-10 and SNOMED-CT. All records are anonymized to eliminate direct identities while maintaining temporal sequence for clinically relevant sequential prediction.
The PROMISE-Eval 2024 dataset consists of over 32,180 patient records with over 5.4 million clinical events, such as diagnoses, operations, prescriptions, and treatment codes. The SemEval-2024 dataset comprises roughly 21,630 patient records with over 3.1 million annotated clinical operations. The frequency of events per patient is inconsistent, illustrating authentic diversity in longitudinal healthcare pathways. All experiments utilize the comprehensive datasets.
Data Segmentation and Leakage Mitigation
Dataset partitioning is conducted exclusively at the patient level to guarantee rigorous evaluation and avert information leakage. The records are partitioned into training, validation, and test sets utilizing an 80–10–10 split ratio. A constant random seed is utilized to ensure the repeatability of the divisions. Each patient is allocated to a single partition, thus avoiding the distribution of correlated events from the same individual across many subgroups and ensuring an unbiased performance evaluation.
Preprocessing Pipeline
All clinical events are standardized and arranged chronologically for each patient to maintain temporal consistency. Infrequent medical codes affecting fewer than ten patients are eliminated to diminish sparsity and enhance statistical stability. Patient histories are converted into structured sequences of coded events appropriate for embedding and sequence-based learning. The processed trajectories are employed for training the plaintext BiLSTM model and for encrypted inference following their conversion into the CKKS-based ciphertext format.
FHE-based Authentication, Signatures, and Access Control
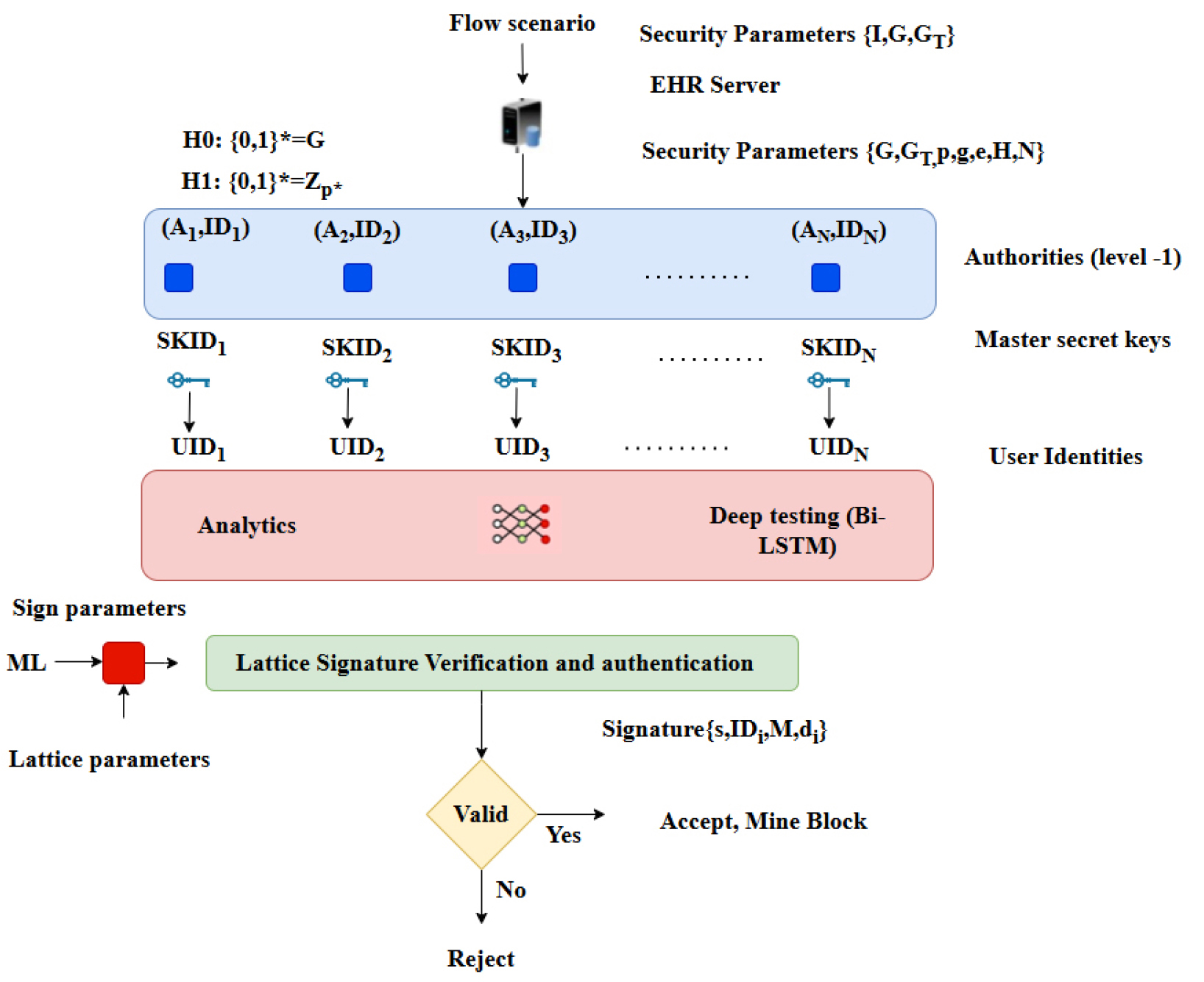
The FHEDaaS framework employs lattice-based cryptographic techniques to provide confidentiality, integrity, and post-quantum resilience for the long- term preservation of medical data in decentralized healthcare systems. The access-control layer aims to reduce insider threats and unlawful privilege escalation by linking permits and operational requests to cryptographic commitments instead of depending on plaintext policy statements. This architecture guarantees that access decisions are upheld via verifiable cryptographic proofs, thus safeguarding sensitive info during permission. The access-control workflow has four fundamental phases: startup, key creation, signature, and verification. During initialization, global public parameters are constructed via Ring- Learning-with-Errors primitives and discrete Gaussian sampling, thereby assuring resilience against both classical and quantum adversaries under conventional lattice hardness assumptions. During the key generation phase, approved healthcare institutions and system entities safely acquire cryptographic key material, comprising public-private key pairs and session-level encryption keys, over authenticated channels that adhere to institutional security regulations.
During the signing step, authorized organizations produce lattice-based digital signatures that cryptographically link operational parameters, role-based attributes, patient consent tokens, and the hash commitment of the encrypted Electronic Health Record payload. This guarantees that all requests to access, amend, or process medical data are distinctly linked to verified identities and consent documents. During the verification phase, the system recalculates the pertinent commitments and authenticates the lattice-based signatures before sanctioning any read or write activity on the blockchain ledger or encrypted storage layer. The suggested solution mitigates the danger of insider leaking and unauthorized privilege misuse by implementing ciphertext-bound permission and verifiable cryptographic commitments. The dependence on lattice-based structures offers post-q uantum security assurances, connecting the framework with enduring confidentiality needs for healthcare data preservation in intelligent and sustainable building contexts.
The Healthcare 4.0 infrastructure made possible by FHEDaaS is seen in Figure 2. Before being sent or processed externally, patient data that has been extracted from EHRs is first encrypted using FHE. After that, a permissioned blockchain ledger oversees the encrypted artifacts, with smart contracts handling auditability, authorization, and consent validation. To make sure that, when doing analytics, no raw patient data is ever revealed, and the encrypted data are immediately processed by the Deep Learning-as-a- Service module. The encrypted prediction outputs produced by the BiLSTM module from the protected clinical sequences can only be deciphered by authorized stakeholders with valid private keys. FHEDaaS employs the CKKS technique for approximation arithmetic over real-valued representations to attain a 128-bit post-quantum security level for encrypted neural inference while striking a balance between efficiency and accuracy. 8192 is the polynomial modulus degree, and 218 bits make up the coefficient modulus chain. This method provides a secure pipeline that is suitable for Healthcare 4.0 predictive analytics from beginning to finish.
FHE Configuration for Privacy-Preserving Neural Inference
A FHEDaaS utilizes the CKKS approximation homomorphic encryption method to facilitate secure real-valued computations for neural inference on encrypted Electronic Health Record sequences. Each patient trajectory is encrypted using the system’s public key before being transmitted to the Deep Learning-as-a-Service layer. All neural computations are performed directly on ciphertexts, and only authorized individuals with the matching private key can decrypt the prediction results. To ensure computational viability, the framework conducts only encrypted inference. Model training occurs on anonymized plaintext data inside a controlled setting, whereas inference is performed on CKKS ciphertexts after deployment. This method maintains data secrecy at the service layer without the excessive computational burden of fully encrypted recurrent network training.
The CKKS configuration employs a polynomial modulus degree of 8192 and a coefficient modulus chain amounting to 218 bits. Security validation is conducted based on established Ring-Learning- with-Errors hardness assumptions utilizing a reputable lattice security assessment methodology. Parameter selection guarantees resilience against both classical and quantum attackers, while preserving a multiplicative depth adequate for encrypted BiLSTM inference without the need for bootstrapping. The selected configuration optimally balances security, accuracy, and computing performance to facilitate privacy-preserving implementation in resource- limited smart building settings. The security of the chosen CKKS parameter set is assessed using a conventional lattice security estimator, and the estimated bit-security is presented in the Results to substantiate the asserted post-quantum security level.
Permissioned Blockchain Framework for Secure EHR Orchestration
The blockchain layer of FHEDaaS is established as a permissioned consortium network utilizing Hyperledger Fabric version 2.2, deployed in a three-node configuration within a Docker environment. System administration and chaincode lifecycle activities are conducted using Node.js version 14.17.0 and npm version 6.14.13.
Smart contracts offer immutable audit trails for electronic health record operations, ensure validation of patient consent, and enforce role-based access control restrictions. To improve scalability and minimize on-chain storage burden, the ledger exclusively records cryptographic hashes, policy metadata, and secure data pointers. Encrypted EHR ciphertexts are retained in a secure off-chain repository, identified by blockchain references. The consortium deployment functions inside a regulated local setting to assess architectural viability and cryptographic integration. This configuration does not emulate network propagation delay or wide-area consensus latency, and so these factors are not extrapolated to large-scale distributed production environments.
Deep Learning as a Service (DLaaS) on Encrypted EHR Trajectories
Electronic Health Records are fundamentally longitudinal, event-oriented, and temporally organized. Each patient record is depicted as a sequential arrangement of standardized clinical codes, including ICD-10 and SNOMED-CT IDs, thus maintaining inter-visit temporal connections. These trajectories are sparse, irregular, and heterogeneous, necessitating a sequential modeling approach that can capture both short-term and long-range contextual interactions. Clinical codes are included with a pretrained 500- dimensional Word2Vec representation developed from extensive clinical corpora. This embedding facilitates the semantic encoding of diagnoses, procedures, and treatment events into dense vector representations, enhancing contextual generalization relative to sparse encodings. The embedding layer is initialized with pretrained weights and subsequently refined during supervised learning.
The predictive framework consists of a Bidirectional Long Short-Term Memory (BiLSTM) network with a hidden state dimension of 128 in each direction. The bidirectional architecture allows the model to understand contextual connections from both preceding and following clinical events, which is essential in longitudinal EHR data because diagnostic patterns often depend on a broader temporal context. L1–L2 regularization is applied with a coefficient of 0.001 to mitigate overfitting, and model optimization is performed using the Adam optimizer with a learning rate of 0.001. Training is conducted for 500 epochs, employing early stopping based on validation loss.
At each time step t, the LSTM cell update can be expressed as:
where represents the integrated clinical-code vector at time step , , and indicate the preceding concealed and cell states, 𝜎σ(ㆍ) denotes the sigmoid function, whereas ⊙ signifies element-wise multiplication. The forward and backward hidden states are amalgamated to generate a contextually informed representation:
In binary clinical prediction, the ultimate sequence representation is converted into a probability:
where may represent the final time step or be aggregated throughout the process. This representation encompasses both prior and subsequent clinical context and is preserved during CKKS-encrypted inference through polynomial approximations of the non-linearities.
The choice of BiLSTM is motivated by its predictive effectiveness and ease of deployment. Longitudinal EHR sequences exhibit temporally linked and irregular patterns, with bidirectional context improving representation quality. Compared to Transformer-based architectures, BiLSTM has reduced parameter complexity and lower multiplicative depth, which is crucial under CKKS-based homomorphic constraints. Increasing the hidden dimension to 256 yielded a minimal improvement in performance (about 1.3% in validation accuracy) while substantially increasing ciphertext multiplication depth and encrypted inference latency. Consequently, the 128-dimensional design provides an optimal balance between predictive performance and homomorphic computation efficiency. Model training is conducted only in the plaintext domain using anonymized and preprocessed sequences, with an 80%–10%–10% division for patient-level training, validation, and testing. Inference is performed exclusively on CKKS- encrypted inputs during operational deployment within the FHEDaaS framework. All intermediate computations are encrypted, and only authorized individuals possessing the appropriate cryptographic credentials can decrypt the final outcomes. This differentiation between plaintext training and encrypted inference ensures excellent stability and rigorous privacy protection. A GRU-based sequence model functions as a lightweight plaintext baseline to confirm that BiLSTM provides superior clinical sequence representation on these datasets, while the encrypted implementation retains BiLSTM because of its accuracy-depth trade-off within CKKS constraints.
Security and Compliance Status
The proposed FHEDaaS architecture amalgamates lattice-based Fully Homomorphic Encryption with a consortium blockchain to ensure confidentiality, integrity, availability, accountability, and non-repudiation for healthcare data in smart building contexts. Instead of depending on a singular administrative entity, security assurances are cryptographically upheld among distributed players. Confidentiality is maintained via CKKS-based homomorphic encryption, which ensures that patient Electronic Health Records remain encrypted during storage, sharing, and outsourced inference, preventing infrastructure operators, cloud service providers, and blockchain validators from accessing plaintext clinical data. Model training occurs on anonymized plaintext data in restricted conditions, while inference during deployment is performed solely on encrypted inputs, thus minimizing the exposure of sensitive medical information. Integrity and non-repudiation are upheld using lattice- based digital signatures and immutable ledger commitments. Every transaction involving encrypted medical data is cryptographically signed by authorized parties and anchored to the consortium blockchain through hash commitments; any attempt at modification alters the cryptographic digest, rendering tampering computationally detectable and facilitating verifiable audit trails appropriate for medical record traceability. Accountability and auditability are attained via smart contract-based access policies and timestamped ledger records, wherein access requests are authenticated against cryptographic commitments and role-specific permissions before approval. As authorization logic operates at the blockchain layer, policy enforcement transcends individual institutional domains, hence mitigating the possibility of cross- organizational collusion. Availability is enhanced via decentralized consortium validation, since distributed ledger replication reduces single points of failure and bolsters resilience in smart building healthcare infrastructures that require high uptime for continuous monitoring. The paradigm adheres to standard regulatory standards for healthcare information systems, particularly on confidentiality, integrity, and auditability, while acknowledging that formal legal compliance is contingent upon the deployment context and institutional governance. The implementation of lattice-based cryptographic primitives significantly improves long-term durability and post-quantum resilience, especially pertinent for prolonged patient record retention durations.
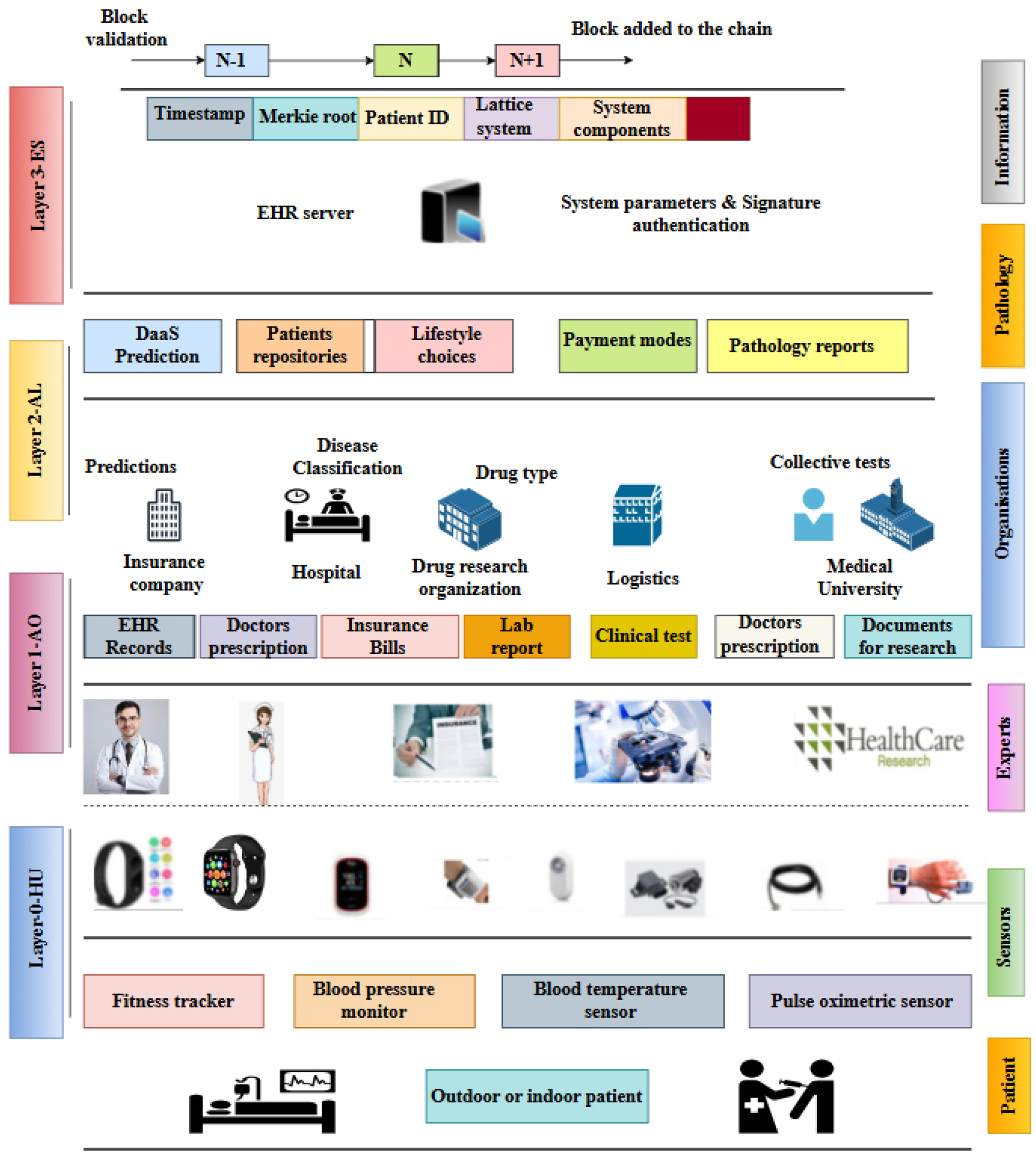
Figure 3 is provided to clarify the hierarchical integration of sensing devices, healthcare organizations, privacy-preserving analytics, and blockchain- based enforcement within the proposed FHEDaaS system. The textual methodology delineates cryptographic security, encrypted inference, and consortium governance individually, whereas the figure integrates these elements into a cohesive operational workflow. This illustrates the conversion of patient- generated signals from wearable devices in smart building settings into organized clinical records, which are encrypted prior to storage or processing and later regulated through blockchain-based authorization. The picture further delineates the distinction between off-chain encrypted data repositories and on-chain cryptographic commitments, therefore underscoring the system’s hybrid architecture. The diagram elucidates the intricate interplay among sensing, organizational processing, service-level analytics, and ledger-based integrity enforcement, thereby contextualizing the maintenance of confidentiality, integrity, auditability, and availability throughout the entire Healthcare 4.0 data lifecycle. This architectural visualization enhances the methodological explanation by elucidating the comprehensive data flow and enforcement mechanisms inside the proposed secure EHR orchestration architecture.
Implementation Details and Reproducibility
All tests are conducted in Python 3.7 utilizing Keras with TensorFlow as the computational backend, and the predictive architecture adheres to the configuration outlined in Table 2. Experiments are performed on a local workstation featuring an Intel i5 CPU and 8 GB RAM, lacking a dedicated GPU, so establishing a consistent baseline for assessing the overhead of encrypted computing. The blockchain framework is implemented with Hyperledger Fabric v2.2, arranged as a three-node consortium network within Docker containers. Smart contract logic and network orchestration are administered using Node.js v14.17.0 and npm v6.14.13 to guarantee predictable chaincode execution and compatibility among peers.
Table 2.
BiLSTM Model Configuration and Training Parameters
The symbolic timing variables in the analytical cost formulations represent empirically measured execution times of the cryptographic primitives utilized in the FHEDaaS framework to evaluate computational and communication overhead. Each fundamental, encompassing hashing, discrete Gaussian sampling, encryption, decryption, and signature verification, is completed 100 times, with average runtimes documented utilizing high-resolution timestamps from the Python time module. Performance assessment includes encrypted inference latency, block commitment delay, data retrieval duration, cryptographic calculation overhead, and communication expenses related to secure transactions. The cryptographic parameters, such as polynomial ring configuration, Gaussian sampling distributions, and lattice dimensions, are constant throughout trials and comply with recognized post-quantum security guidelines to guarantee scientific consistency and repeatability.
Performance Evaluation
Accuracy in predictions, computing costs, and communication costs are three ways to evaluate the proposed FHEDaaS system. When applied to the Healthcare 4.0 setting, these key performance indicators (KPIs) give a comprehensive evaluation of the system’s efficacy, security, and extensibility. To identify the reasons of latency, the Results presents three configurations: plaintext BiLSTM inference, FHE BiLSTM inference without blockchain, and the whole FHEDaaS pipeline with smart contract permission and blockchain commitment.
Prediction Accuracy Metrics
Traditional confusion matrix measurements like True Negatives (TN), False Positives (FP), as well as True Positives (TP) are used to evaluate the encrypted analytics module’s prediction accuracy based on Bi-LSTM. This job’s primary outcomes are binary classifications. The letters TP, TN, FP, and FN represent properly recognized, wrongly predicted, and missed sickness cases, respectively, and correctly identified non-illness cases, respectively. They serve as the foundation for measures that are more precise when combined.
Precision:
Prediction accuracy may be measured by dividing the total number of accurate and wrong forecasts by the total number of right predictions; this ratio is called precision. A higher accuracy score indicates that the system produces fewer false alarms. This is essential in therapeutic decision-making, hence avoiding unnecessary treatments for patients.
Recall (Sensitivity):
The ability of the system to detect actual cases of disease is assessed by recall. Increased memory rates reduce the likelihood of overlooking people requiring healthcare, hence enhancing the patient-centric safety of healthcare 4.0 applications.
F1-score:
The F1-score serves as a metric that balances accuracy and recall, offering a singular value that reflects the model’s predictive ability. This offers a significant benefit when addressing unbalanced datasets, because it reduces the likelihood of bias in judgment resulting from false positives and negatives.
System Workflow and Interaction Model
During system operation, pseudonymized Electronic Health Record sequences originating from healthcare information systems and smart building medical sensing infrastructures are first processed within the Data Ingestion module. After preprocessing and structural validation, sequences are encrypted using the system’s Fully Homomorphic Encryption public key before leaving the trusted institutional boundary. A lattice-based digital signature mechanism binds each ciphertext to patient consent tokens and role-based policy commitments, ensuring authenticity and enforceable authorization.
Encrypted medical payloads are stored in an off-chain repository to preserve scalability, while the consortium blockchain maintains cryptographic hash commitments, access control metadata, and permission proofs. This separation ensures that no plaintext clinical data is recorded on-chain while still providing tamper-evident traceability and integrity guarantees.
When predictive analytics services are requested, smart contracts verify the requester’s identity, role attributes, and consent parameters prior to authorizing access to the encrypted data reference. Upon successful validation, the Deep Learning as a Service module performs BiLSTM-based inference directly over CKKS-encrypted inputs. All intermediate computations remain encrypted throughout execution. The prediction output is returned in encrypted form and may only be decrypted locally by the authorized stakeholder using the corresponding private key.
Each encryption event, access request, inference execution, and data retrieval action generates an immutable blockchain record linking permission validation, ciphertext references, and computational operations. This workflow enforces confidentiality during outsourced analytics while preserving integrity, accountability, availability, and non-repudiation across distributed healthcare entities operating within smart building environments.
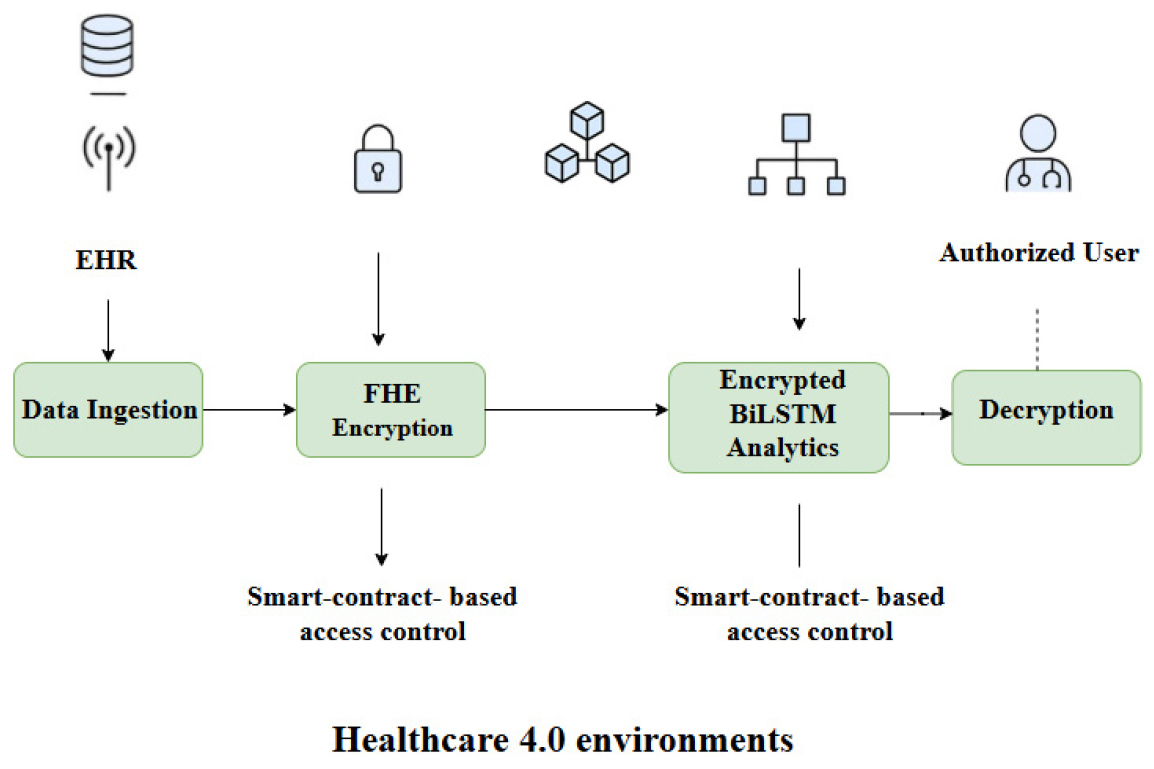
Figure 4 is provided to visually encapsulate the operational data flow of the FHEDaaS system, from ingestion to the decryption of allowed results. The approach delineates encryption, blockchain governance, and encrypted inference in distinct subsections, but the picture integrates these processes into a unified interaction sequence. It delineates the distinction between encrypted computation and access control enforcement, emphasizing the function of smart contracts in governing data utilization within Healthcare 4.0 contexts. The graphic elucidates the maintenance of confidentiality throughout processing, while accountability is guaranteed through blockchain- based authorization and audit tracking.
Computational Cost Metrics
The estimate of the computational load of FHEDaaS takes into account the cryptographic phase’s necessary for safe EHR processing. The execution time of cryptographic primitives, which involves several processes, is expressed in milliseconds.
Initialization Phase
Building cryptographic frameworks and creating critical parameters are part of this phase. Due to the inclusion of all hashing, Gaussian sampling, ECC, symmetric encryption, as well as R-LWE computation techniques, this stage is the most resource-intensive.
Key Generation Phase
Secure generation and transmission of symmetric keys takes place now. Ensuring the secure exchange of keys across consortium members is essential, but less complex than initialization.
Signature Generation Phase
At this point, the legitimacy of EHR transactions is confirmed by signing papers. If executed correctly, signing transactions will not impede throughput.
Signature Verification Phase
Data integrity and non-repudiation are guaranteed via signature verification. The cost significantly increases with each transaction, making it a crucial metric for scalability.
Communication Costs Metrics
Communication overhead encompasses the cryptographic exchanges required for the secure transmission of IDs, nonces, encrypted tokens, and promises. In practice, communication costs should preferably be expressed in bytes and optionally transformed into time using connection bandwidth; nonetheless, the subsequent expressions are preserved as originally stated to consistently represent the measured overhead components.
Initialization Communication Cost
Modular exponentiation, R-LWE methods, Gaussian samples, and ECC transactions all get their parameters in this step. This technique specifies the highest possible communication load that may be experienced during the system setup process, taking into account all necessary cryptographic components.
Key Generation Communication Cost
Gaussian samples and the results of symmetric encryption are the only data that may be sent throughout the key creation procedure. This offers a lightweight and very secure method of exchanging keys, that must be satisfied before the strategy may be widely implemented in healthcare facilities.
Signature Generation Communication Cost
The translation of signed messages, hashes, as well as Gaussian outputs is part of the λόγo communi- cation overhead. In healthcare transactions, their effectiveness is vital for enabling the simultaneous and safe communication of data between doctors and patients.
Signature Verification Communication Cost
This stage requires sharing Gauss samples, modular inverse results, and hash values. Due to higher transmission expenses, the healthcare blockchain network’s response time falls as the number of verification requests grows.
The evaluation of FHEDaaS offers a thorough picture of efficiency and usefulness, which examines forecast accuracy, calculation costs, and communication costs. Communication measurements demonstrate that dispersed blockchain networks may expand, computation metrics demonstrate the utility of cryptographic operations, and prediction metrics demonstrate the clinical reliability of encrypted deep learning. Everyone agrees that the framework is simple to use in the healthcare industry due to the harmony it can achieve between security, accuracy, and efficiency settings for 4.0.
Results Analysis and Discussion
This section presents the prediction performance and system-level overhead to assess FHEDaaS in Healthcare 4.0 smart building environments. In addition to traditional classification metrics, latency ablation is also included that distinguishes the runtime costs of plaintext BiLSTM inference, FHE-based encrypted inference without blockchain, and the complete FHEDaaS workflow, which encompasses smart-contract permission and blockchain commitment. The validation of security parameters is presented for the chosen CKKS configuration using a conventional lattice security estimator to substantiate the asserted security level. Ultimately, scalability trends are examined utilizing standard workload metrics and present variability data from numerous executions to guarantee robustness and reproducibility. To support model selection, the BiLSTM model is compared with a lightweight GRU baseline in plaintext, examining the accuracy-cost trade-off that necessitates the retention of BiLSTM for encrypted deployment.
The predictive efficacy of the BiLSTM and GRU models was assessed utilizing plaintext EHR sequences through a 5-fold cross-validation technique, with results delineated in Table 3. The BiLSTM model exhibits enhanced predictive performance, attaining a mean precision of 0.882, a recall of 0.781, and an F1-score of 0.828, with negligible variability among folds, indicating reliable bidirectional temporal learning in patient trajectories. The GRU baseline demonstrates marginally inferior metrics, with an accuracy of 0.823, recall of 0.729, and F1-score of 0.772, suggesting that although GRU captures sequential relationships, it is less adept than BiLSTM in modeling intricate longitudinal patterns. The counts of true positives and true negatives underscore the enhanced classification reliability of the BiLSTM, whilst the rates of false positives and false negatives are lower than those of the GRU, this displays the right choice to maintain BiLSTM for encrypted inference deployment in FHEDaaS. The five-fold standard deviations demonstrate consistent performance and strong generalization across various patient subsets, validating the use of BiLSTM for future homomorphic encrypted prediction tasks.
Table 3.
Plaintext Model Comparison and Predictive Performance (5-Fold Cross-Validation)
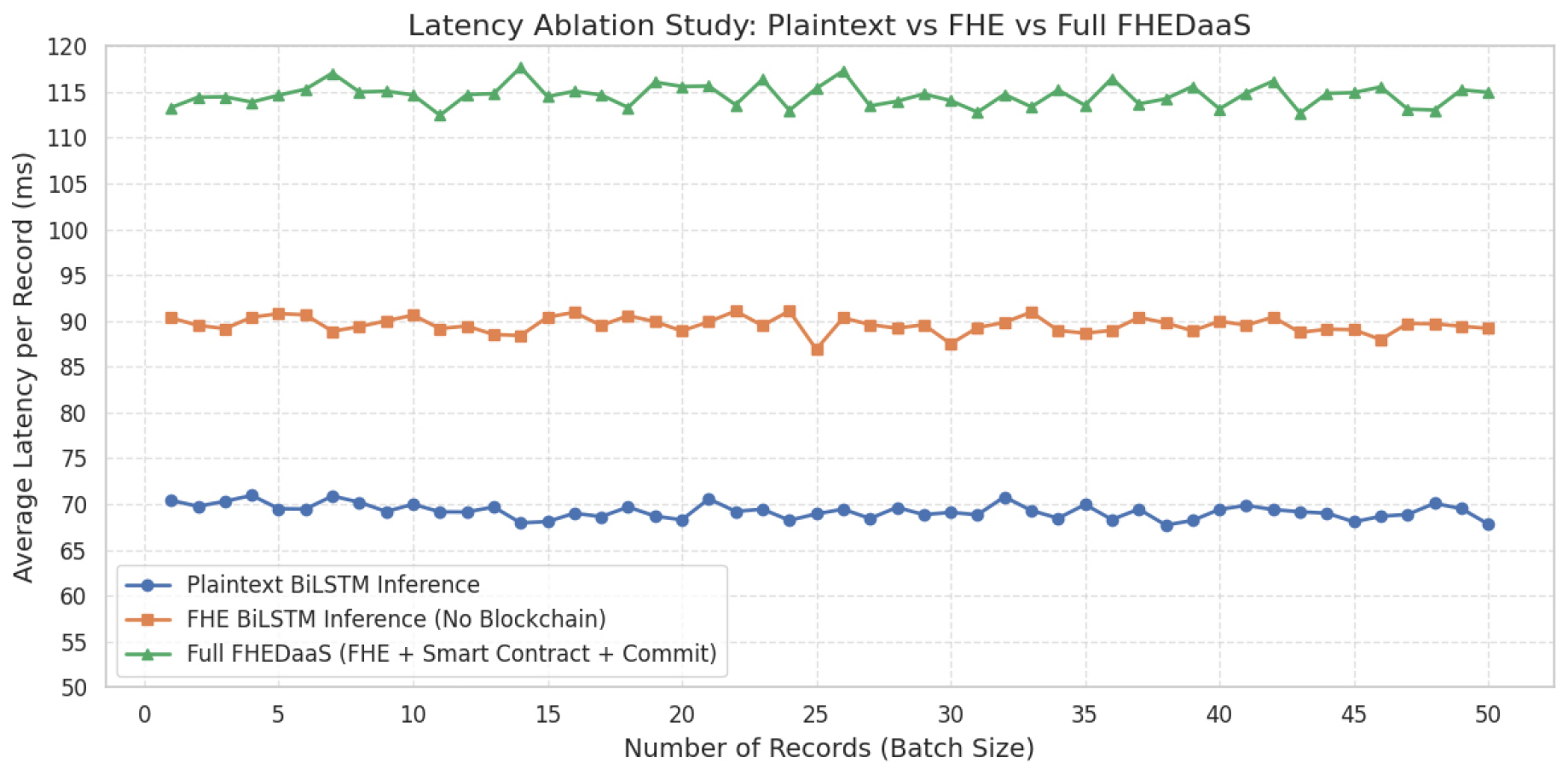
Figure 5 illustrates a latency ablation study contrasting plaintext BiLSTM inference, CKKS- encrypted BiLSTM inference devoid of blockchain connectivity, and the comprehensive FHEDaaS process that incorporates smart-contract authorization and blockchain commitment. Latency is expressed as the mean processing duration per record across escalating batch sizes. Plaintext inference incurs the least computational expense, while CKKS-based encrypted inference entails significant yet manageable overhead stemming from ciphertext encoding, homomorphic multiplications, rotations, rescaling, and noise-budget management inherent to lattice- based arithmetic. The complete FHEDaaS configuration demonstrates a minor latency increase due to smart contract execution and ledger commitment, indicative of the governance cost associated with auditable access control. The three curves exhibit stability over batch sizes without significant divergence, demonstrating consistent scaling behavior within the established testbed design. Latency results are shown as averages from several executions within the local consortium environment, and the observed variability was minimal under the constant experimental conditions, hence reinforcing the repeatability of the stated overhead trends.
Security and Computational Analysis
Computational overhead
To quantify the cryptographic overhead imposed by FHEDaaS, the execution duration of the primary security primitives associated with initialization, key generation, signature generation, and signature verification is assessed. Table 4 presents the average execution time of each primitive assessed on the experimental platform. Hashing and Gaussian sampling incur minimal yet recurrent expenses, whereas modular exponentiation and ECC multiplication constitute comparatively substantial elements utilized in authentication and key exchange. Ring operations denote polynomial arithmetic employed in lattice- based frameworks and CKKS-related computations. These measurements offer an empirical perspective on the security overhead necessary for ensuring confidentiality, integrity, and access accountability in privacy-preserving healthcare analytics, subsequently utilized to analyze end-to-end runtime when integrated with encrypted inference and blockchain.
Table 4.
Computation Times of Cryptographic Operations
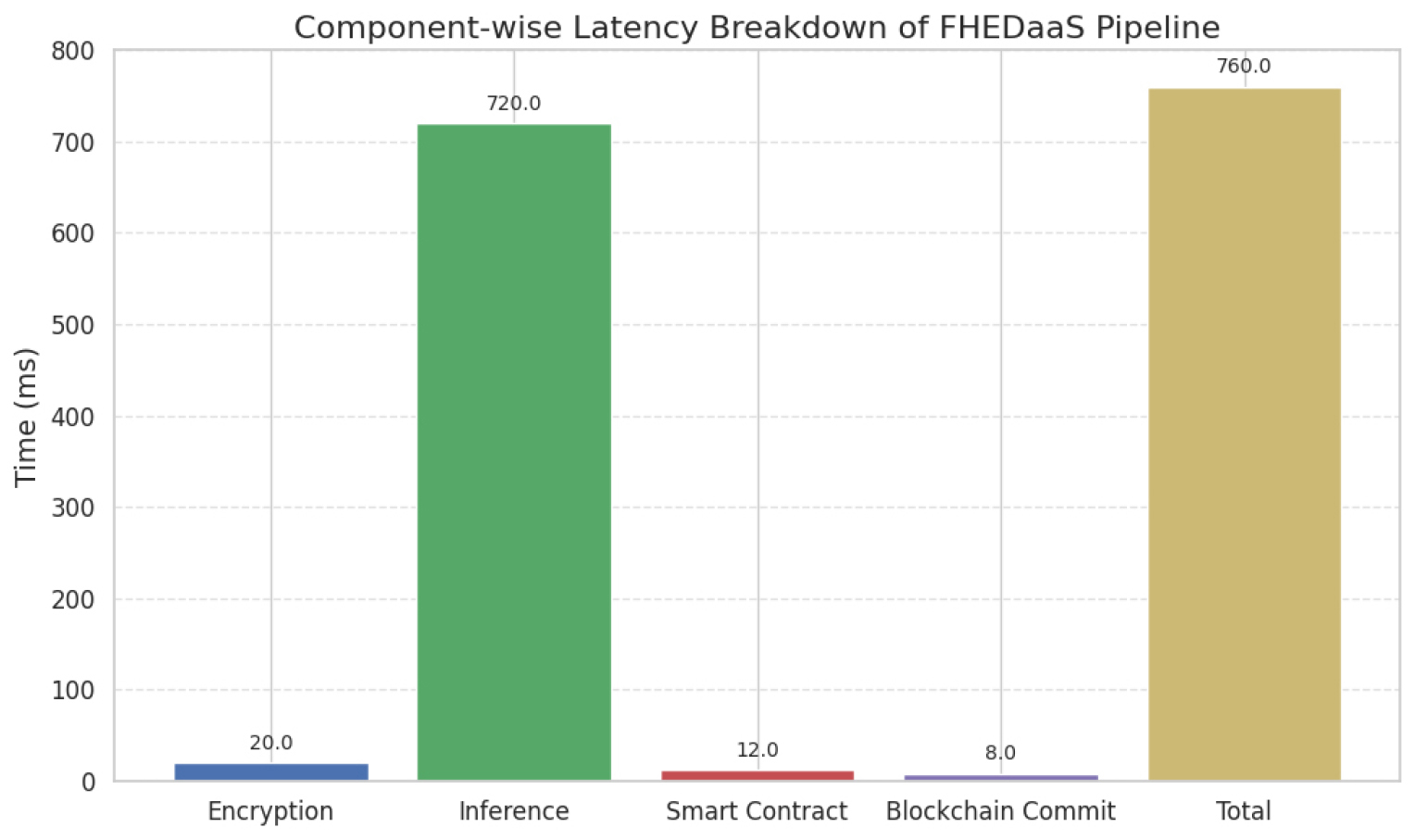
Figure 6 illustrates a component-specific analysis of the end-to-end latency of the FHEDaaS pipeline in a CKKS-encrypted deployment. The encrypted inference phase constitutes the majority of execution time, averaging around 720 ms per record, indicative of the computational expenses associated with ciphertext encoding, homomorphic multiplications, rotations, rescaling operations, and noise control intrinsic to lattice-based arithmetic. The encryption phase incurs a minimal overhead of around 20 ms, signifying input encoding and ciphertext preparation. The validation of smart contracts and the commitment to blockchain bring extra latencies of around 12 ms and 8 ms, respectively, suggesting that decentralized authorization and ledger finalization impose relatively modest overhead compared to homomorphic computing. The total latency of roughly 760 ms indicates that encrypted neural inference is the primary cost factor, however blockchain governance methods provide manageable and foreseeable overhead appropriate for auditable Healthcare 4.0 implementations.
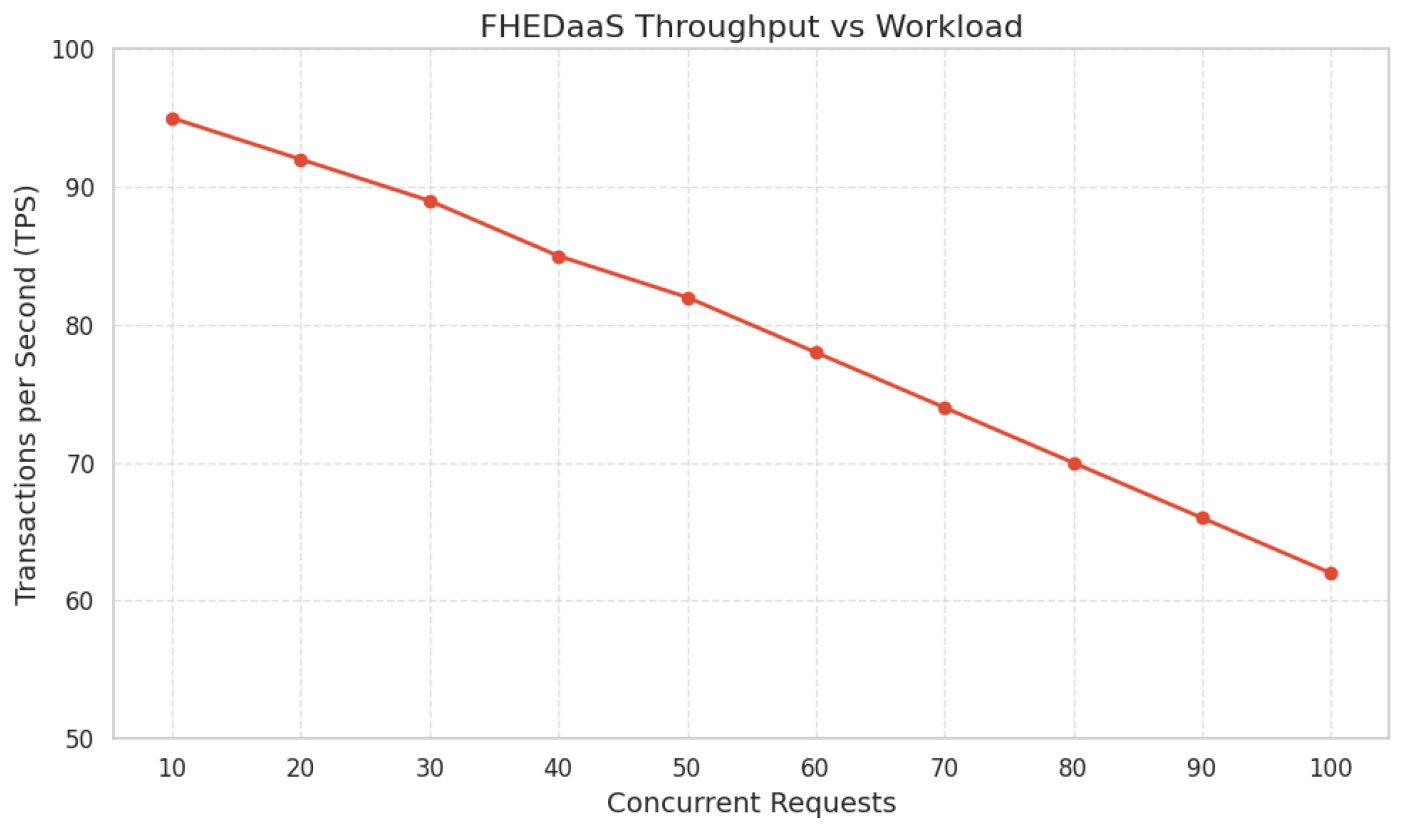
Figure 7 depicts the throughput performance of FHEDaaS as concurrent request demands escalate. Throughput diminishes progressively from roughly 95 transactions per second at low concurrency to around 62 transactions per second at elevated concurrency levels. This reduction signifies anticipated contention effects resulting from cryptographic processing, smart contract validation, and consensus-related processes under increased load. The consistent and gradual reduction in throughput signifies steady scaling behavior, devoid of sudden performance deterioration or system failure within the assessed range. This predictable behavior is vital in healthcare monitoring settings, where consistent reaction to fluctuating workloads is crucial. The observed pattern indicates that while privacy-preserving computation and blockchain coordination impose quantifiable overhead, transaction processing capacity stays within operationally acceptable thresholds for multi-user Healthcare 4.0 implementations.
Initialization Stage
Initialization includes two ring procedures pertinent to RLWE, symmetric encryption, ECC operations for auxiliary key exchange, modular exponentiation, hashing, and Gaussian sampling. The startup cost is determined by measured primitive runtimes.
Key generation, which includes symmetric-key establishment and Gaussian sampling, necessitates:
Signature creation, which involves a ring operation with hashing and Gaussian sampling, necessitates:
Signature verification, which entails hashing, Gaussian sampling, and two modular inverses, necessitates:
The aggregate computing time per transaction across all phases is thus:
Communication Cost
Communication latency is documented as end-to- end transfer delay in the experimental testbed, encompassing message preparation, serialization, and local Docker-based messaging among consortium nodes.:
∙Initialization: 0.0771 seconds (77.1 milliseconds)
∙Key Generation: 0.00615 seconds (6.15 milliseconds)
∙Signature Generation: 0.00440 seconds (4.40 milliseconds)
∙Signature Verification: 0.00925 seconds (9.25 milliseconds)
∙Total latency associated with communication: 0.0969 seconds (96.9 milliseconds).
These numbers represent the local testbed environment and indicate the message-handling overheads within the consortium. The introduction of WAN may incur supplementary delays, which fall beyond the parameters of this measurement.
A holistic perspective on the concepts of utility and efficiency has been formed based on the assessment of FHEDaaS, where the assessment of the forecast accuracy, computational complexity, and communication complexity has been done. The units of communication illustrate the scalability of the spread blockchain network, the units of computation illustrate the practical utility of the operation of cryptography, while the units of prediction illustrate the medical usability of the use of the encrypted deep-learning process. These findings indicate that the system achieves a practical balance between security, predictive accuracy, and computational efficiency, supporting its feasibility for Healthcare 4.0 deployments.
Table 5 compares plaintext BiLSTM inference with CKKS-encrypted BiLSTM inference to assess the privacy-performance trade-off engendered by homomorphic execution. The predictive metrics remain consistent with those reported in the plaintext evaluation, with precision, recall, and F1-score maintained at 0.882, 0.781, and 0.828, respectively, due to the application of the same trained BiLSTM parameters and identical decision threshold during deployment. Encryption solely influences the representation of inputs and intermediate calculations, not the semantics of the learned model. Conversely, the average inference latency escalates from 71.3 ms per record in plaintext to 720.0 ms per record under CKKS, resulting in an approximate 10× increase. The increase is warranted due to the supplementary processes necessitated in ciphertext-domain execution, encompassing CKKS encoding and scaling, ciphertext packing, iterative polynomial multiplications and rescaling across network layers, as well as rotation and relinearization operations essential for vectorized computations, alongside the growth-management overhead intrinsic to lattice-based arithmetic within finite modulus chains. The chosen value aligns with CPU-only homomorphic inference in limited settings that eschew bootstrapping, yet where ciphertext operations continue to be much more costly than plaintext arithmetic. The findings correspond with existing anticipations that Fully Homomorphic Encryption (FHE) incurs substantial computational overhead compared to plaintext processing, while facilitating confidentiality-preserving inference appropriate for Healthcare 4.0 contexts necessitating encrypted outsourcing and auditable access control.
Table 5.
Performance Benchmark of Plaintext vs CKKS-Encrypted BiLSTM Inference
Table 6 delineates a system-level ablation that distinguishes the latency and resource contributions of plaintext inference, CKKS-encrypted inference, and blockchain-facilitated authorization and commitment. Plaintext inference yields the minimal per-record delay and maximal throughput, as execution is conducted using conventional arithmetic on unencrypted data sequences. The FHE-only option segregates the overhead from ciphertext encoding, packing, and CKKS arithmetic, resulting in increased per-record latency and diminished throughput due to the elevated computational intensity of lattice-based operations. The comprehensive FHEDaaS configuration incurs supplementary yet limited overhead due to smart contract validation and ledger commitment, leading to a slight increase in delay compared to FHE-only execution and a consequent decrease in throughput. Peak memory increases significantly in encrypted configurations due to the considerable storage demands of ciphertext representations, evaluation keys, and intermediate encrypted buffers compared to plaintext tensors. The analysis indicates that encrypted inference is the primary cost factor, whereas blockchain governance adds a minor added expense that facilitates auditability and policy enforcement in Healthcare 4.0 implementations.
Table 6.
Latency Ablation Table
Table 7 delineates the CKKS configuration employed for privacy-preserving neural inference and underpins the asserted security claim. The polynomial modulus degree and coefficient modulus chain dictate the difficulty of the underlying Ring-LWE issue and limit the permissible noise budget for homomorphic computation. The chosen scale regulates numerical precision for approximation calculations and is set to optimize decoding accuracy while managing noise escalation during encrypted evaluation. The target multiplicative depth indicates the maximum number of consecutive ciphertext multiplications allowed before decryption failure occurs, and the setting is chosen to enable encrypted inference without bootstrapping, which would otherwise significantly increase latency. Documenting these parameters in conjunction with an estimator-based security level facilitates transparent validation of post-quantum security assertions and allows for replicable comparisons with alternative privacy-preserving healthcare analytics solutions.
Table 7.
CKKS Security Parameter Validation
Discussion
The findings demonstrate that the proposed Privacy- Preserving Blockchain Healthcare Systems for Healthy and Sustainable Smart Buildings framework successfully attains the desired equilibrium between predictive utility and privacy enforcement within a limited testbed deployment. The comparison of plaintext models indicates that BiLSTM offers superior longitudinal representation learning compared to the GRU baseline, with precision increasing from 0.823 to 0.882, recall from 0.729 to 0.781, and F1-score from 0.772 to 0.828. This indicates an enhancement of roughly 7.2 percent in precision, 7.1 percent in recall, and 7.3 percent in F1-score, justifying the choice to maintain BiLSTM for subsequent encrypted deployment when sequence dependencies between visits retain clinical significance. The latency ablation elucidates system behavior. Plaintext inference is the most expedient, but CKKS-encrypted inference incurs significant overhead from ciphertext encoding, packing, rotations, rescaling, and noise-budget management. The complete FHEDaaS pipeline introduces only a minimal additional delay beyond FHE-only execution, suggesting that smart-contract permission and ledger commitment include relatively insignificant governance costs in comparison to homomorphic computation. Throughput diminishes due to encryption and blockchain coordination, anticipated from increased CPU-bound computational intensity and transaction orchestration; nonetheless, the reduction is modest, indicating robust scaling within the assessed workload range. The innovation is evident in the cohesive orchestration of three typically distinct components: CKKS-based encrypted inference, permissioned blockchain auditability with consent enforcement, and a Healthcare 4.0 tiered smart- building deployment context that explicitly connects sensing, organizational processing, encrypted analytics, and tamper-evident governance. Limitations encompass dependence on a local consortium testbed that fails to account for wide-area network latencies and the implementation of encrypted inference without comprehensive encrypted training, potentially constraining assertions of end-to-end encrypted learning.
Conclusion and Future Work
The proposed study illustrates that privacy- preserving clinical prediction and auditable access governance can be concurrently achieved in Healthcare 4.0 smart building environments by integrating CKKS-based homomorphic inference with a permissioned blockchain enforcement layer. The BiLSTM predictor demonstrates superior predictive accuracy compared to a GRU baseline in plaintext evaluation, signifying enhanced modeling of irregular longitudinal EHR trajectories. Encrypted deployment maintains identical decision-making behavior while incurring anticipated homomorphic latency overhead, with ablation results indicating that the majority of runtime costs stem from ciphertext-domain inference rather than blockchain governance. The incorporation of a CKKS parameter validation table enhances the reliability of the asserted security configuration and facilitates replication. A practical deployment scenario entails ongoing surveillance in intelligent healthcare environments, where data from wearables and sensors is transformed into structured records, encrypted prior to outsourcing, and analyzed through encrypted inference, with access and audit trails regulated by smart contracts. Future research should assess multi-site and wide-area contexts, incorporate supplementary clinical tasks and calibration analyses, investigate model compression or polynomial approximation to diminish homomorphic depth and latency, and enhance governance with more comprehensive consent policies and emergency override mechanisms, accompanied by formal verification to bolster real- world applicability.
Declarations
Ethical Approval: Ethical approval does not apply to this article.
Competing interests: The authors declare that they have no competing interests.
Authors’ contributions: All authors are the main authors of the current paper. Mainly Yogesh Kushwaha and Niranjan Lal contributed to developing the ideas, design of the study, theory. Further, Manisha Manjul contributed to results analysis, and paper writing. And finally, all authors contributed for reading and approving the final manuscript.
Funding: Not Applicable.
Availability of data and materials: Data will be made available at the reasonable request of the authors.